When a single engineer walked out of SSA with 500 million Americans' Social Security records on a thumb drive, centralized data custody catastrophically failed. Individual data sovereignty replaces that broken model with cryptographic vaults where you hold the keys to your own identity. No single breach can ever compromise 500 million records again because no single system holds them.
When a single engineer walked out of SSA with 500 million Americans' Social Security records on a thumb drive, centraliz
Core Promise · What It Does · Core Purpose
Business Model Perspective
Strategic Value The fundamental failure exposed by the SSA breach is architectural, not procedural. When one engineer with elevated access can exfiltrate the entire NUMIDENT database, the problem is not insufficient background checks or access controls; it is the existence of a monolithic database containing 500 million records in the first place. Individual data sovereignty addresses this root cause by distributing custody to the data subjects themselves. Under this architecture, SSA would hold verifiable credentials issued to each individual's vault rather than a centralized database vulnerable to bulk exfiltration. The user grants granular, purpose-limited, revocable consent for each access. This transforms the trust model from 'trust the institution' to 'verify the math' through cryptographic proofs that are mathematically auditable. Value capture analysis confirms this approach dramatically lifts user capacity from a severity-2 baseline to 7-8, channeling existing high motivation from anxiety into agency (source: value capture and MCOA analysis).
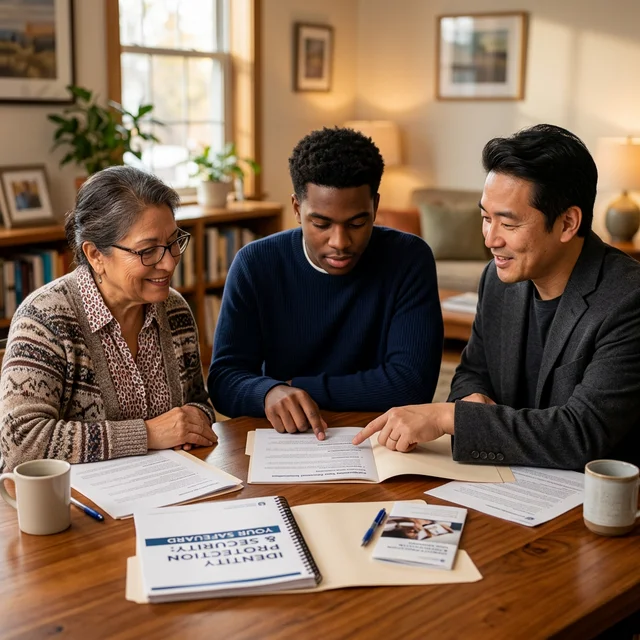
Marketing Perspective
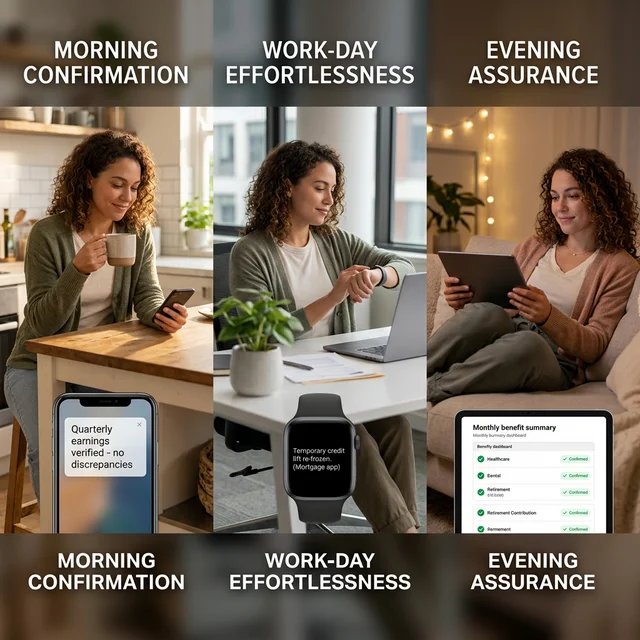
Core Capabilities Three interlocking capabilities form the product architecture. First, the user-owned data vault with cryptographic custody eliminates the single-point-of-failure that made the breach possible. You hold the encryption keys; no institution, no government agency, and no rogue engineer can access your data without your cryptographic authorization. Second, granular consent and purpose-limited access control ensures that sharing one data field does not unlock others. Each disclosure is independently authorized with purpose constraints and automatic expiration. This transforms the permanent exposure of immutable data like birthdate and birthplace from a lifelong vulnerability into a manageable, compartmentalized risk. Third, cross-system identity verification and anomaly detection replaces the impossible manual forensics of comparing records across SSA, IRS, credit bureaus, and banks. Automated reconciliation catches discrepancies within seconds, catching unauthorized modifications within minutes rather than months (source: hero strengths analysis, scores 23, 21, and 20).
Strategic Questions
Why This Matters Now The breach exposed data that cannot be changed: your Social Security number, date of birth, birthplace, parents' names, citizenship status, and race/ethnicity. Unlike a credit card number, these identifiers are permanently compromised. Every American with SSA records is affected, and the existing response toolkit is wholly inadequate. Current credit monitoring services cost $10-40 per month and provide only reactive detection, discovering fraud only after damage occurs. There is no mechanism for individuals to determine whether their specific records were accessed. There is no way to revoke the government's access to data you were legally compelled to provide. The institutional trust that was violated was not voluntary; Americans are required by law to furnish their SSN for employment, taxes, and benefits. Individual data sovereignty exists because the centralized custody model has proven it cannot protect the data it compelled citizens to hand over. The only durable solution is one where no single point of failure can compromise an entire population's identity (source: task analysis and UVP).
Sources & Evidence
- UVP analysis: individual data sovereignty as centralized custody alternative
- Task analysis: 500M+ Americans, NUMIDENT database, SSN/DOB/birthplace/citizenship/race/parents' names
- Hero strengths: Strength 1 (Score 23) cryptographic vault, Strength 2 (Score 21) granular consent, Strength 3 (Score 20) cross-system verification
- Value capture verdict: moderate value capture, capacity lift from 2 to 7-8
- MCOA analysis: motivation strong (severity 5), capacity critically weak without intervention